Decentralised networks such as Bitcoin and Ethereum have the potential to revolutionize many different industries thanks to their secure, transparent and immutable properties allowing for a decentralised way to store data and transfer value. The current limitations of these networks are the scalability and performance challenges they face. The Bitcoin network can handle 7 transactions per second, the Ethereum network can handle 20 whilst the Visa network can process over 24,000 transactions per second. Reaching mass adoption requires these decentralised networks to have the capability to match or exceed the traditional centralised networks.
These limitations are being actively addressed throughout the blockchain industry with the introduction of additional layer 1 networks, “side chains” and “layer 2” networks.
Layer 1 Networks and Side Chains
The creation of additional layer 1 networks (“side chains”) is analogous to creating a new blockchain similar to the Bitcoin or Ethereum network. This means an entirely different blockchain is created which contains its own blocks and transactions so over time these tend to run into the same problems other decentralised networks have solved through time, most notably how to secure the network. Anyone can create a new layer 1 network and choose some consensus algorithm such as proof-of-work or proof-of-authority but since these networks have a low number of participants it is possible for single entities to compromise the immutability of the network. The primary advantage of side-chain networks is that they are separate from other decentralised networks and therefore free from congestion.
Side chains have their place in the blockchain industry and tend to do quite well when the primary layer 1 networks are congested. However, since they are effectively entirely different blockchains there is always a need for users to have the ability to transfer assets between them. The challenge here is that both blockchains run independently of each other and as such, there is no way to pass data between the networks in a decentralised way (“on-chain”).
This is commonly resolved by using a cross-chain bridge consisting of a trusted entity operating on both networks. Users can transfer assets to the trusted entity (usually a smart contract), the bridge operator submits this deposit onto the side-chain (also usually a smart contract) and synthetic assets are minted at a 1-to-1 ratio. This means users can transfer their assets between networks with ease however since there is no direct on-chain communication the weakest chain in the link is the trusted entity.
The diagram below demonstrates this process:
Note that since the synthetic asset is backed by real assets on the layer 1 network, the price of the asset remains closely correlated on the side-chain.
The disadvantage of having a trusted entity is that users must trust that this entity will not become compromised and must also trust the implementation of the bridge is secure. The trusted entity could submit false information on the side-chain and mint an infinite number of synthetic assets.
There have been many instances of cross-chain bridges becoming compromised, notable examples include:
- Axie Infinity’s bridge which failed due to the validators becoming compromised.
- Nomad Bridge which failed due to the poor smart contract implementation.
- Harmony Bridge hack which also failed due to the validators becoming compromised.
Notable examples of side chains include Polygon PoS, Gnosis Chain and Loom Network.
Layer 2 Networks
Layer 2 networks are similar to side chains in that they also maintain their own blockchain however the key difference is that they are self-contained within a larger layer 1 network. This allows increased transaction throughput without sacrificing decentralisation or security since these are properties inherited from the layer 1 network.
Running a blockchain within a larger layer 1 blockchain is possible by bundling transactions together and submitting the resulting data into the larger blockchain (state changes). This allows for the larger layer 1 to handle important properties such as security, data availability and decentralisation whilst allowing layer 2 to focus on solving for scalability.
The diagram below shows how this can be achieved. Note the “Layer 1/2 Communication Bridge” is simply a smart contract deployed on the layer 1 network responsible for passing messages between the two blockchains.
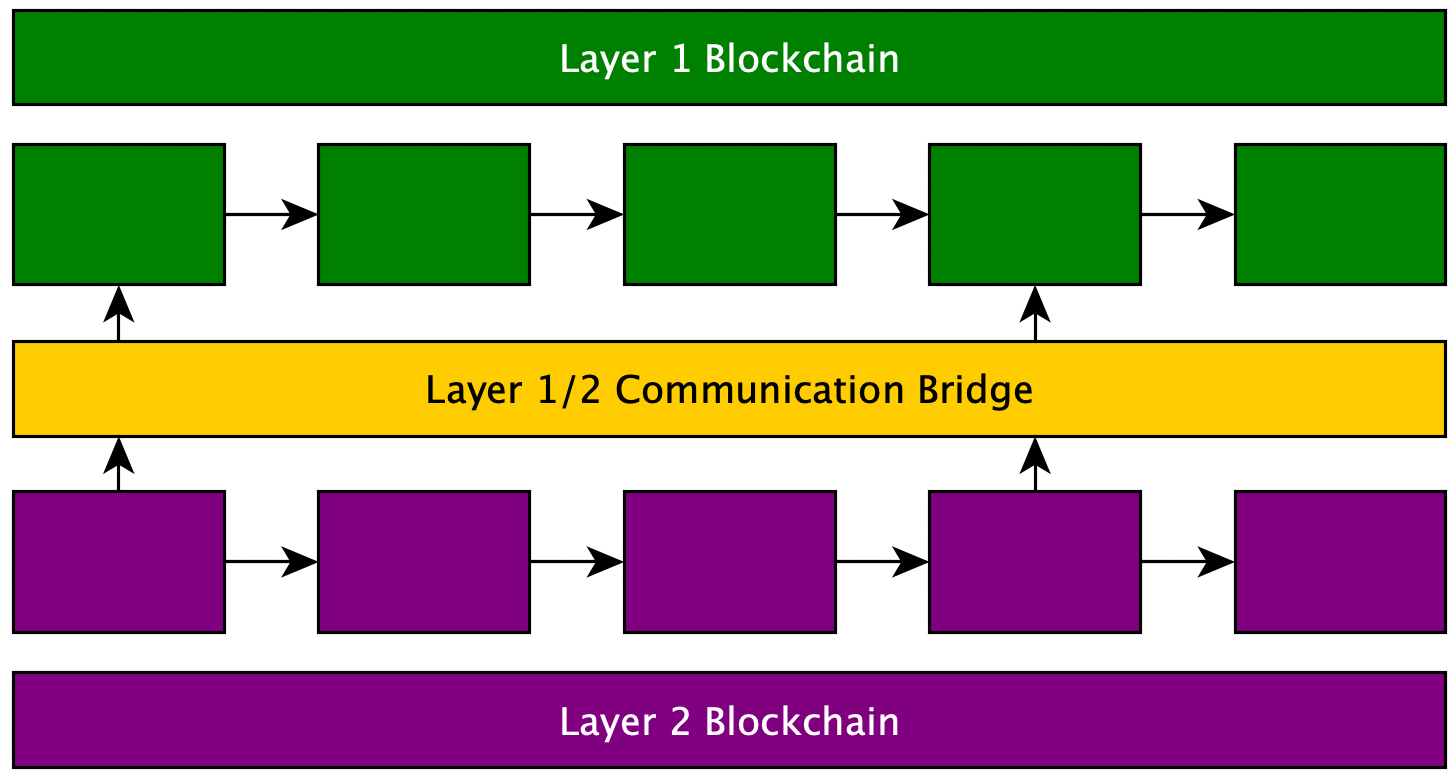
This architecture allows for periodic updates from the layer 2 blockchain to be submitted into the layer 1 network by batching transactions together and only submitting the resulting changes (state). This architecture also allows for any data to be passed between the two chains which result in a decentralised approach to bridging assets.
This means when a user wants to transfer an asset from layer 1 to layer 2, the process remains largely the same as demonstrated with side chains, however, there is no longer a need for the trusted party since data can be passed between these two chains in a decentralised way.
The major decision layer 2 network architecture must design for is how transactions are batched together and submitted to the layer 1 network. There are currently two well-known methods to do this which are currently in use by layer 2 networks: Optimistic Rollups and Zero-Knowledge Rollups.
Optimistic Rollups
This process consists of bundling together many transactions into batches and submitting the resulting state change to the layer 1 network. This optimistic approach allows for the possibility of invalid transactions being embedded into the rollup. Invalid transactions can be combated by implementing a “challenge period” which is simply an amount of time when anyone can provide a fraud-proof to the network and if accepted, the roll-up protocol re-executes the transactions and updates the roll-up state (batch) accordingly.
The disadvantage of this approach is the challenge period introduced for communications between the two layers which results in a delay for any cross-chain communication such as bridging assets. This “challenge period” is currently 7 days which means it is possible for transactions to be reverted at any time within this period. This is a core security mechanism designed to keep funds safe.
Optimism (blockchain network) is currently using optimistic rollups and you can read more about the challenge period in their documentation.
Zero Knowledge Rollups
This process is very similar to optimistic rollups in that many transactions are put into batches and the resulting state change is submitted to the layer 1 network. The key difference is in how these transactions are bundled together to provide security and finality.
Zero Knowledge Rollups (zk-Rollups) achieve additional security and finality by using zero-knowledge proofs which mathematically prove transactions are valid and the resulting state change of batch of transactions is valid. You can read more about zero-knowledge proofs here.
This approach for rolling up transactions offers added security and speed when it comes to sending data between chains and ensuring submitted transactions are valid. There is therefore no “challenge” period required when using zk-Rollups.
zk-Sync and Arbitrum currently use zk-Rollups to offer added security and transactional speed.
Summary
Blockchain networks such as Bitcoin and Ethereum have scalability issues which limit their ability to process transactions at scale. The two solutions we looked at today consisted of the creation of additional layer 1 networks (side-chains) and the design and development of layer 2 networks which periodically submit their state onto the layer 1 network allowing the network to inherit the security properties of the larger layer 1 network. Both of these techniques help to increase transaction throughput but they also have their own trade-offs and limitations that must be considered primarily decentralisation and security.

